Aurelia Salzano ed Emanuela D’Ambrosio
The alchemist of fashion.
È questo il titolo della mostra curata dagli appassionati studenti del Master in Art Management e Curating Art and Fashion di Istituto Marangoni Firenze in collaborazione con il WP Store fiorentino, che dal 2014 ha acquisito parte dell’archivio storico di Gian Franco Ferré.


Questa esposizione celebra l’uomo e l’artista percorrendo e narrando tutte le fasi e le contaminazioni del suo processo creativo, in cui confluiscono una commistione di elementi chiave alla base della sua produzione artistica.


Natura, viaggi, medioevo, architettura.
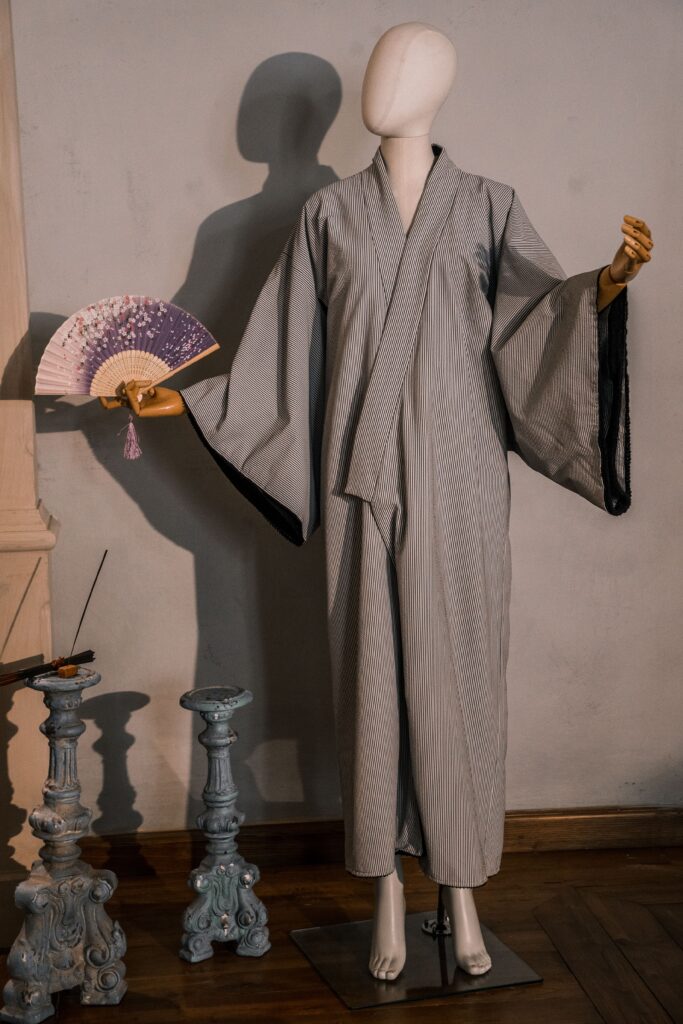
Attraverso una selezione accurata di capi iconici, bozzetti originali, oggetti raccolti durante i suoi viaggi e volumi d’arte ci si trova immersi in uno spazio che racconta il dietro le quinte del suo lavoro, in una dimensione intima, dalle luci calde e soffuse, dove anche la sua stessa scrivania diviene oggetto di culto che lascia ben immaginare l’architetto, l’uomo e l’artista intento nel suo lavoro.


Dal dialogo con gli studenti è emersa la complessità e la delicatezza con cui sono stati selezionati gli elementi più rappresentativi di una personalità così poliedrica, da cui ne consegue il titolo di “Alchimista della moda”.